Outbound NAT in pfSense - source NAT configuration
Outbound NAT (source NAT) in pfSense controls source address translation for traffic leaving the network through an external interface. When a packet from an internal host is directed to the internet, the firewall replaces the private source address with the public address of the WAN interface (or another specified address). This is the fundamental mechanism that enables internal hosts with RFC 1918 private addresses to access internet resources.
pfSense provides four outbound NAT modes that differ in the degree of automation and control. The choice of mode is determined by the complexity of the network infrastructure and translation requirements.
Operating modes
pfSense supports four outbound NAT modes. Switching between modes is performed under Firewall > NAT, on the Outbound tab.
| Mode | Description | When to use |
|---|---|---|
| Automatic | Automatic rule generation for all internal interfaces | Standard configurations with a single WAN |
| Hybrid | Automatic rules + ability to add manual rules | Specific exceptions needed (static port, multi-WAN) |
| Manual | Only manually created rules | Full control over translation |
| Disable | Outbound NAT completely disabled | Networks with routable addresses |
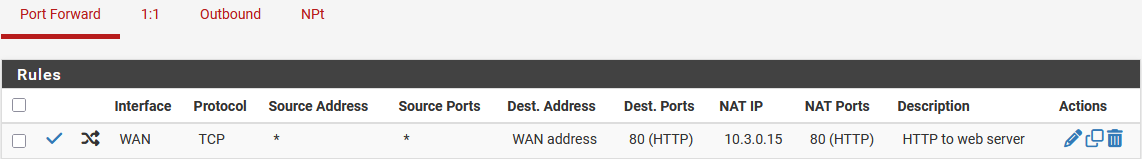
Fig. 1. Outbound NAT mode selection
Mode comparison
| Characteristic | Automatic | Hybrid | Manual |
|---|---|---|---|
| Automatic rules | Yes | Yes (as fallback) | No |
| Manual rules | Ignored | Processed first | Only source of rules |
| Response to new interface | Automatic | Automatic (for fallback) | Manual rule addition required |
| Configuration complexity | Minimal | Moderate | High |
| Risk of connectivity loss | Minimal | Low | High (on error) |
| Recommended for | Basic configurations | Most production systems | Complex multi-interface configurations |
Automatic mode
Automatic mode (Automatic Outbound NAT) is the default setting after pfSense installation. In this mode, the firewall independently creates outbound NAT rules for each combination of internal interface and subnet.
Automatically generated rules perform the following translations:
- Traffic from LAN, OPT1, OPT2, and other internal interface subnets is translated to the WAN interface address.
- VPN client traffic (OpenVPN, IPsec) is translated to the WAN address.
- A rule for localhost (127.0.0.0/8) is generated with the ISAKMP port (500) and the static port flag for correct IPsec operation.
Automatic rules are displayed in the interface as read-only entries. They cannot be modified or deleted - only viewed.
Automatic mode is suitable for most simple configurations. Switching to a different mode is necessary when at least one of the following conditions exists:
- Static port is required for specific hosts or protocols.
- Multiple WAN interfaces are used with different translation rules.
- Specific subnets must be bound to particular external addresses.
Hybrid mode
Hybrid mode (Hybrid Outbound NAT) combines the advantages of automatic and manual modes. Automatic rules continue to be generated and serve as a base (fallback), while manual rules are added on top and processed with higher priority.
Processing order in hybrid mode:
- Manual rules are checked first (top to bottom).
- If no manual rule matches, automatic rules are checked.
Hybrid mode is recommended for most production configurations. It allows adding specific rules (static port for SIP, subnet binding to a particular WAN) without the need to manually maintain the complete rule set.
Typical hybrid mode workflow:
- Switch the mode to Hybrid Outbound NAT.
- Click Save, then Apply Changes.
- Create a manual rule for the specific exception (for example, static port for a SIP server).
- All remaining traffic continues to be processed by automatic rules.
Manual mode
Manual mode (Manual Outbound NAT) gives the administrator complete control over outbound NAT rules. All automatic rules are removed, and only manually created rules are used.
Warning:
When switching to manual mode, pfSense will offer to copy the current automatic rules as a starting point. It is strongly recommended to accept this offer. If the copy is declined and no rules are created manually, all outbound traffic will cease to be translated, and internal hosts will lose internet access.
Manual mode is necessary in the following cases:
- A completely non-standard translation configuration is required.
- Precise control over rule processing order is needed.
- Complex setups with multiple WAN interfaces, VPNs, and specific translations are in use.
- A “Do not NAT” rule is needed for certain traffic (for example, traffic between VPN segments).
When a new interface or subnet is added in manual mode, NAT rules are not created automatically. The administrator must add the corresponding rules manually; otherwise, traffic from the new interface will not be translated.
Creating a rule
Step-by-step configuration
- Navigate to Firewall > NAT, select the Outbound tab.
- Verify that Hybrid or Manual mode is selected.
- Click Add to create a new rule.
Fig. 2. Outbound NAT rule list
- Configure the rule parameters:
General parameters
| Field | Description | Example |
|---|---|---|
| Interface | Outbound interface (where traffic is directed) | WAN |
| Address Family | Address family | IPv4 |
| Protocol | Protocol (any for all) | Any |
| Source | Source address or subnet | 192.168.1.0/24 |
| Source port | Source port (usually Any) | Any |
| Destination | Destination address | Any |
| Destination port | Destination port | Any |
Translation parameters
| Field | Description | Example |
|---|---|---|
| Translation Address | Address to which the source is translated | Interface Address |
| Translation Port | Translation port or port range | (empty for automatic) |
| Static Port | Preserve the original client source port | Unchecked |
| Pool Options | Address selection method from pool (when using an alias) | Default |
Additional parameters
| Field | Description |
|---|---|
| Disabled | Disable the rule without deleting it |
| Do not NAT | Mark traffic for exclusion from translation |
| No XMLRPC Sync | Do not synchronize the rule in HA configurations |
| Description | Description of the rule’s purpose |
- Click Save, then Apply Changes.
Translation Address options
- Interface Address - address of the outbound interface (WAN IP). The most common option.
- Virtual IP - a specific VIP address created on the outbound interface. Used for binding a subnet to a particular public address.
- Alias - a group of addresses for load distribution. Combined with Pool Options, it provides balancing across multiple external addresses.
- Other Subnet - an arbitrary subnet for translation.
Pool Options
When using an alias or subnet in Translation Address, the following distribution methods are available:
| Method | Description |
|---|---|
| Default | Round Robin without address persistence |
| Round Robin | Sequential cycling through addresses |
| Round Robin with Sticky Address | Round Robin with client-to-address persistence |
| Random | Random address selection from the pool |
| Random with Sticky Address | Random selection with address persistence |
| Source Hash | Deterministic selection based on source address hash |
| Bitmask | Address masking (used for /24-to-/24 translations) |
Common scenarios
Static port for SIP and VoIP
SIP, IKE (IPsec), and some gaming protocols require the original source port to be preserved during translation. By default, pfSense randomizes ports to enhance security, which breaks these protocols.
Configuring static port in hybrid mode:
- Switch Outbound NAT to Hybrid mode.
- Create a rule:
- Interface - WAN
- Source - SIP server or phone address (for example,
192.168.1.200/32) - Destination - Any
- Translation Address - Interface Address
- Static Port - checked
- Description - “Static port for SIP PBX”
- Save and apply changes.
For IPsec VPN initiated by the firewall itself, pfSense automatically creates a rule with static port for UDP 500 (ISAKMP) and UDP 4500 (NAT-T) in automatic and hybrid modes.
Warning:
The Static Port flag is incompatible with using a single external address for multiple internal hosts sharing the same source port. If two SIP phones simultaneously initiate connections from port 5060, a conflict will occur. In such cases, each device should be assigned a separate VIP through individual rules.
Binding a subnet to a specific WAN address
In configurations with multiple WAN interfaces or additional public addresses, it may be necessary for a specific internal subnet to access the internet through a particular external address.
Example: the server subnet 10.0.2.0/24 should use VIP 203.0.113.20 instead of the primary WAN IP.
- Create VIP
203.0.113.20on the WAN interface (Firewall > Virtual IPs). - Switch Outbound NAT to Hybrid mode.
- Create a rule:
- Interface - WAN
- Source -
10.0.2.0/24 - Destination - Any
- Translation Address -
203.0.113.20(select the VIP from the list) - Description - “Server subnet outbound via VIP”
- Save and apply.
All other traffic will continue to be translated to the WAN IP through automatic rules.
Multi-WAN and policy-based NAT
When using multiple WAN interfaces (multi-WAN), each WAN requires its own outbound NAT rules. In automatic and hybrid modes, pfSense creates rules for each WAN interface automatically.
When traffic from a specific subnet needs to be directed through a particular WAN (policy routing):
- Create a gateway or gateway group under System > Routing.
- Create a firewall rule on the internal interface specifying the gateway (Gateway field).
- In hybrid or manual outbound NAT mode, verify that a rule exists for the corresponding WAN interface and source subnet.
Do not NAT rule
In some scenarios, specific traffic must be excluded from translation:
- Traffic between VPN segments using private addresses.
- Traffic to peer networks through a GRE tunnel.
- Traffic to networks routed without NAT.
To create an exclusion:
- Create an outbound NAT rule with the Do not NAT flag checked.
- Specify the source subnet in the Source field.
- Specify the target subnet for which translation is not required in the Destination field.
- Place the rule above the rule that performs translation for this traffic.
Troubleshooting
Internet lost after switching to manual mode
The most common issue is switching to manual mode without creating the necessary rules or declining the offer to copy automatic rules.
Resolution:
- Navigate to Firewall > NAT > Outbound.
- Switch the mode back to Automatic or Hybrid.
- Click Save, then Apply Changes.
- Verify that internet access is restored from internal hosts.
If access to the web interface is lost, connect to the firewall console (serial port or physical console) and execute:
# Reset outbound NAT to automatic mode
pfctl -d && pfctl -e -f /tmp/rules.debugAlternatively, use the console menu: the Reset to factory defaults option as a last resort.
Static port not working
Symptoms: SIP phone registers but calls do not connect; IPsec Phase 1 does not establish.
Verification:
- Ensure the rule with Static Port is positioned above the general NAT rule for the given subnet.
- Verify that the rule specifies the correct source address (a specific host rather than the entire subnet if the issue concerns a single device).
- Check the state table (Diagnostics > States) - the source port should match the port in the translation.
- Confirm that the Static Port flag is checked in the outbound NAT rule, not in the firewall rule.
# Verify NAT rules in pf
pfctl -s nat
# Check state table for SIP traffic
pfctl -ss | grep 5060Multi-WAN: traffic exits through the wrong WAN
When using multiple WAN interfaces, traffic may be translated through the wrong address.
Verification:
- Ensure the firewall rule on the internal interface has the correct Gateway (the specific WAN gateway).
- Verify that an outbound NAT rule exists for the target WAN interface and source subnet.
- In manual mode, verify that rules exist for each WAN interface.
- Check gateway status under Status > Gateways - a failed gateway will cause failover to the backup WAN.
Diagnostic commands
# View all outbound NAT rules loaded in pf
pfctl -s nat
# Check which external address is used for a specific internal host
pfctl -ss | grep 192.168.1.100
# Verify NAT translation in real-time
tcpdump -i em0 src host 192.168.1.100 -n
# Test outbound address from the server
curl -4 ifconfig.meMigration from other platforms
Cisco ASA
In Cisco ASA, dynamic NAT (PAT) is configured through NAT objects (versions 8.3+) or global NAT (before 8.3).
ASA 8.3+ (Object NAT, PAT):
object network INSIDE-SUBNET
subnet 192.168.1.0 255.255.255.0
nat (INSIDE,OUTSIDE) dynamic interfaceASA 8.3+ (Twice NAT with address pool):
nat (INSIDE,OUTSIDE) source dynamic INSIDE-SUBNET PAT-POOL
object network PAT-POOL
range 203.0.113.10 203.0.113.15pfSense equivalent:
- For standard PAT through the WAN IP - automatic outbound NAT mode (default configuration).
- For PAT through an address pool - hybrid or manual mode with VIP addresses and a rule using an alias in Translation Address with Pool Options set to Round Robin.
Key difference: in ASA, dynamic NAT configuration combines translation and control through ACLs. In pfSense, outbound NAT and firewall rules are independent entities.
FortiGate
In FortiGate, outbound NAT is implemented through an IP Pool in the firewall policy.
Standard PAT (overload):
config firewall policy
edit 1
set srcintf "lan"
set dstintf "wan1"
set srcaddr "LAN-SUBNET"
set dstaddr "all"
set action accept
set nat enable
next
endPAT through IP Pool:
config firewall ippool
edit "OUTBOUND-POOL"
set startip 203.0.113.10
set endip 203.0.113.15
set type overload
next
end
config firewall policy
edit 1
set srcintf "lan"
set dstintf "wan1"
set srcaddr "LAN-SUBNET"
set dstaddr "all"
set action accept
set nat enable
set ippool enable
set poolname "OUTBOUND-POOL"
next
endIn FortiGate, NAT is an attribute of the firewall policy. In pfSense, outbound NAT is configured separately from firewall rules, providing a clearer separation of translation and filtering functions.
MikroTik RouterOS
In MikroTik RouterOS, outbound NAT is implemented through a masquerade or src-nat rule in the srcnat chain.
Masquerade (analogous to automatic mode):
/ip firewall nat
add chain=srcnat out-interface=ether1 action=masqueradeSource NAT with a fixed address:
/ip firewall nat
add chain=srcnat src-address=192.168.1.0/24 out-interface=ether1 \
action=src-nat to-addresses=203.0.113.10Differences during migration:
masqueradein MikroTik automatically uses the outgoing interface address (analogous to Interface Address in pfSense).src-natwith a specifiedto-addressesis equivalent to an outbound NAT rule with a specific Translation Address.- In MikroTik RouterOS, NAT and firewall rules are in different chains of the same
/ip firewalltable. In pfSense, NAT and firewall are completely separate pf subsystems.
Related sections
- Port forwarding - redirecting inbound traffic to internal servers
- 1:1 NAT - bidirectional address translation and its interaction with outbound NAT
- NAT overview in pfSense - NAT processing order and interaction between translation mechanisms
- Firewall rules - creating filtering rules and policy routing