OpenVPN Client Export in pfSense - Config and Installers
The OpenVPN Client Export package in pfSense automates the generation of client configuration files and installers based on the parameters of a running OpenVPN server. Rather than manually assembling .ovpn files and copying certificates, administrators obtain ready-to-distribute packages for every major platform: Windows, macOS, Linux, iOS, and Android. This eliminates errors inherent in manual configuration and significantly reduces onboarding time for new VPN users.
The export utility operates exclusively with servers configured in Remote Access mode (SSL/TLS or SSL/TLS + User Auth). Site-to-site tunnels do not support client export, as both sides of the tunnel require manual configuration.
Installing the Package
The openvpn-client-export package is not included in the base pfSense installation and must be installed separately through the package manager.
- Navigate to System > Package Manager > Available Packages.
- Enter
openvpn-client-exportin the search field. - Click Install next to the package, then confirm the installation.
- Wait for the process to complete - this typically takes 10-30 seconds depending on connection speed.
After installation, a new Client Export tab appears under VPN > OpenVPN.
Warning:
Before using the export utility, the OpenVPN remote access server must be fully configured: CA created, server certificate issued, user certificates generated, and the server instance itself configured. Without a functioning server, the export tab will not display any available configurations. Refer to Remote Access Server for complete server setup instructions.
Export Options
The VPN > OpenVPN > Client Export tab presents global export options at the top of the page. These settings apply to all exported configurations.
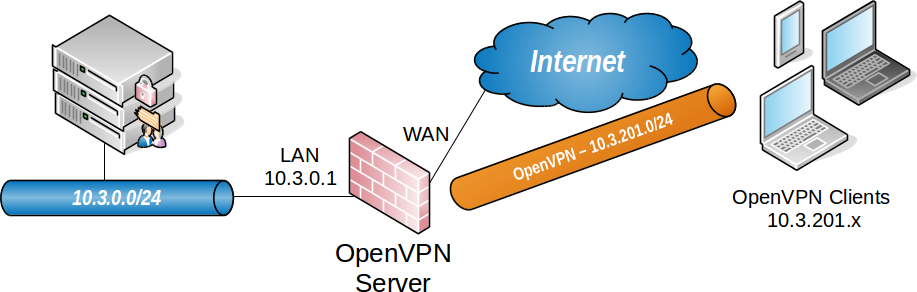
Fig. 1. Global client export configuration options
Server Selection
The Remote Access Server dropdown specifies which OpenVPN server instance the client configurations will be generated for. Only servers operating in Remote Access mode are listed.
Host Name Resolution
The Host Name Resolution setting determines the address placed in the remote directive of exported client configurations. Available options:
| Option | Description | Use Case |
|---|---|---|
| Interface IP Address | WAN interface IP address of pfSense | Static external IP |
| Automagic Multi-WAN IPs | Automatic remote directives derived from port forward rules | Multi-WAN with multiple ISPs |
| Automagic Multi-WAN DDNS | DDNS entries associated with port forward rules | Multi-WAN with dynamic addresses |
| Installation Hostname | Hostname from System > General Setup | Hostname registered in public DNS |
| Dynamic DNS Hostname | DDNS entry configured on pfSense | Single ISP with dynamic IP |
| Other | Custom IP address or FQDN | NAT in front of pfSense, non-standard deployments |
For typical single-ISP deployments with a dynamic IP address, select Dynamic DNS Hostname. For static addresses, use Interface IP Address.
Additional Connection Settings
| Setting | Description |
|---|---|
| Verify Server CN | Controls server certificate Common Name verification via verify-x509-name. Automatic detection is recommended |
| Block Outside DNS | Forces VPN-provided DNS servers on the client. Relevant for Windows 10 and later, where DNS query leaks can occur |
| Legacy Client | Generates directives compatible with OpenVPN 2.4.x for clients that do not support 2.5+ |
| Silent Installer | Adds silent installation flags to the Windows installer. Useful for mass deployment through GPO or SCCM |
| Use Random Local Port | Client uses a random source port. Recommended to allow simultaneous connections to multiple VPNs |
Certificate Options
| Setting | Description |
|---|---|
| PKCS#11 Certificate Storage | Enables hardware token and smart card support for certificate storage |
| Microsoft Certificate Storage | Stores certificates in the Windows certificate store instead of files on disk |
| Password Protection | Password-protects the PKCS#12 file or Viscosity bundle |
Proxy Configuration
When clients need to connect through an HTTP proxy, specify the proxy type, address, port, and optional authentication credentials. These parameters are embedded in exported configurations as the http-proxy directive.
Custom Directives
The Additional configuration options field accepts arbitrary OpenVPN directives that will be appended to every exported configuration. For example:
ping 10
ping-restart 60
hand-window 90Each directive occupies a separate line. Syntax follows the standard OpenVPN configuration file format.
Export Types
The package provides several export formats targeting different platforms and client applications.
| Export Type | Format | Platforms | Details |
|---|---|---|---|
| Inline Configurations | .ovpn | Windows, macOS, Linux | Single file with embedded certificates and keys. Universal format |
| Inline Configurations (Android) | .ovpn | Android | Optimized for OpenVPN for Android |
| Inline Configurations (OpenVPN Connect) | .ovpn | iOS, Android | Optimized for the OpenVPN Connect application |
| Bundled Configurations | .zip | Windows, macOS, Linux | Archive containing separate files: configuration, TLS key, PKCS#12 |
| Configuration File Only | .ovpn | All | Configuration file without embedded certificates |
| Windows Installer (2.5.x) | .exe | Windows 10/11 | OpenVPN GUI installer with embedded configuration. 64-bit and 32-bit versions |
| Windows Installer (2.4.x) | .exe | Windows 7/8/10 | For legacy systems that do not support OpenVPN 2.5+ |
| Viscosity Bundle | .visc.zip | macOS, Windows | Package for the Viscosity client (commercial application) |
Choosing the Right Format
- Standard deployment: Inline Configuration (
.ovpn) - works with any OpenVPN client on any platform. - Mass Windows deployment: Windows Installer with Silent Installer enabled - allows VPN client installation via GPO without user interaction.
- Mobile devices: Inline Configuration (OpenVPN Connect) - the file imports directly into the OpenVPN Connect app on iOS or Android.
- Corporate macOS environment: Viscosity Bundle - when the organization uses the Viscosity client.
- Elevated security requirements: Bundled Configuration with PKCS#12 and password protection - certificates are password-protected, preventing configuration use if the file is compromised.
Per-User Export
Below the global settings, the page displays a list of clients available for export. The list contents depend on the server authentication mode:
- SSL/TLS: all user certificates issued by the CA specified in the server configuration are shown.
- SSL/TLS + User Auth: users from the local database or external directory who have associated certificates are shown.
Each user has access to all export formats. Clicking the corresponding download link generates a file containing the certificate and private key for that specific user.
A search field at the top of the client list enables quick lookup when the certificate list is large.
Warning:
If expected users are missing from the export list, verify the following: the user has an assigned certificate, the certificate was issued by the same CA specified in the OpenVPN server settings, and the certificate has not been revoked in the CRL (Certificate Revocation List).
Configuring Connection Parameters
Overriding the Connection Address
In deployments where pfSense sits behind a NAT device or load balancer, the external VPN address differs from the address on the pfSense interface. In this scenario, select Other in the Host Name Resolution field and manually enter the external IP address or FQDN.
DNS Servers in Exported Configurations
DNS servers pushed to VPN clients are configured in the OpenVPN server settings, not in the export parameters: VPN > OpenVPN > Servers > Edit > DNS Server 1-4. The export package automatically includes the configured DNS servers in generated configurations.
Custom Directives
Parameters specified in the Additional configuration options field are appended to the end of every exported configuration file. This allows administrators to enforce routes, configure keepalive intervals, or specify options not available in the graphical interface.
Example of common additional directives:
# Prevent DNS leaks on Windows
block-outside-dns
# Force all traffic through VPN
redirect-gateway def1
# Set connection timeout
connect-timeout 30Saving Default Settings
The Save as default button at the bottom of the options block persists the current export settings. On subsequent visits to the tab, the saved values are restored automatically. This is convenient when regularly issuing configurations to new users.
Distributing Configurations to Clients
Exported files contain the user’s private key and certificate, making them security-critical assets. The following practices must be observed when distributing configurations to end users:
Secure delivery channel. Configuration files must be transmitted only through encrypted channels: corporate email with encryption, a secure file-sharing service, or in-person delivery on a physical medium. Transmission via unencrypted messengers or public file-sharing platforms is unacceptable.
Password protection. When using the Bundled Configuration or Viscosity Bundle format, enable the Password Protection option. This provides an additional layer of defense if the file is compromised.
Single-use links. When in-person delivery is not feasible, use single-use link services with time and download count restrictions.
Revocation upon compromise. If a configuration file is suspected of being compromised, immediately revoke the user’s certificate through System > Certificates and add it to the CRL associated with the OpenVPN server.
User instructions. Accompany the configuration file with brief import instructions: for Windows - install OpenVPN GUI and place the file in
C:\Users\<user>\OpenVPN\config\; for macOS - import into Tunnelblick or Viscosity; for mobile devices - import through OpenVPN Connect.
Troubleshooting
No Users Appear in the Export List
Common causes:
- The user does not have an assigned certificate. Check in System > User Manager > Users > Edit User > User Certificates.
- The certificate was issued by a different CA than the one specified in the OpenVPN server settings.
- The certificate has been revoked and is present in the CRL.
- The OpenVPN server is configured in Peer-to-Peer mode rather than Remote Access mode.
Exported Configuration Fails to Connect
- Verify that the address in the
remotedirective of the.ovpnfile is reachable from the external network. Runtelnet <address> <port>from the client device. - Confirm that a firewall rule on the pfSense WAN interface permits incoming traffic on the OpenVPN port (default: UDP 1194).
- If pfSense is behind NAT, verify that port forwarding is correctly configured on the upstream router.
- Review OpenVPN logs: Status > OpenVPN on the server side; client logs are accessible through the client application interface.
Certificate Mismatch
The errors TLS Error: TLS handshake failed or VERIFY ERROR indicate a certificate problem:
- The server certificate must be of type Server Certificate, not User Certificate.
- Client and server certificates must be issued by the same CA.
- Certificates must not be expired - verify validity dates in System > Certificates.
- The TLS key (static key) must match between the server and the exported configuration. If the TLS key is regenerated on the server, all client configurations must be re-exported.
Windows: Silent Installation Failure
When deploying the Silent Installer via GPO, the installer may fail if:
- Group Policy prohibits TAP driver installation without administrator confirmation. Add the TAP driver publisher certificate to the Trusted Publishers store.
- Antivirus software blocks the installation. Add an exception for the OpenVPN installer.
Related Sections
- Remote Access Server - complete OpenVPN server setup, CA and certificate creation
- Site-to-Site Tunnel - connecting sites via OpenVPN
- IPsec Mobile Clients - alternative VPN option for mobile devices without additional software installation